In computer networking, the TCP/IP model and the OSI model get referenced a lot, and you can’t get around it if you want to get into computer networking.
Therefore, in this article, I am going to cover how the TCP/IP model is built up and how it works.
Table of contents:
What is the TCP/IP model?
The TCP/IP (Transmission Control Protocol / Internet Protocol) model standardizes computer networking and helps to understand how data transmission works over networks of computers. Its purpose is to make communication over larger distances possible.
The TCP/IP model is based on the OSI model and comprises multiple layers that are numbered from bottom to top. What exactly those layers are and how they work will be discussed in the following.
The original TCP/IP model
Nowadays, we use an updated version of the TCP/IP model. However, I quickly want to cover the layers of the original one to compare them to the updated one later on:

As I already mentioned, the layers are numbered from bottom to top. In fact, that order does play a role because it determines how the computer encapsulates (packs) or decapsulates (unpacks) data.
When sending data, the computer encapsulates it going from top to bottom (Application Layer -> Transport Layer -> . . .)
When receiving data, the computer decapsulates it going the other way around (Link Layer -> Internet Layer -> . . .)
Next, I am going to cover what the layers do and why we need them:
Application Layer
The application layer is closest to the user and directly interacts with an application that sends or receives data using the TCP/IP model. Specifically, at this layer, we specify an application protocol.
Some examples of application protocols would be HTTP, FTP, SSH, and SMTP.
Transport Layer
At the transport layer, we again have to decide between two protocols – TCP (Transmission Control Protocol) and UDP (User Datagram Protocol).
Those two protocols determine how the data is going to be transmitted. – “Do we need a fast or reliable connection?”, “Do we want a connection-oriented or connectionless protocol?”, etc.
Additionally, this layer adds the source and destination ports.
If you want some more details on TCP and UDP, you can have a look at this related article.
Internet Layer
The second layer of the original TCP/IP model handles IP addressing and routing. This layer includes the source IP address and the destination IP address.
Link Layer
The link layer (also known as network access layer) is the slowest layer of the TCP/IP model.
It uses Cables, Switches, Bridges, Repeaters, and Hubs to physically connect to other devices.
Also, it is responsible for mapping logical IP addresses to physical MAC addresses.
The updated TCP/IP model
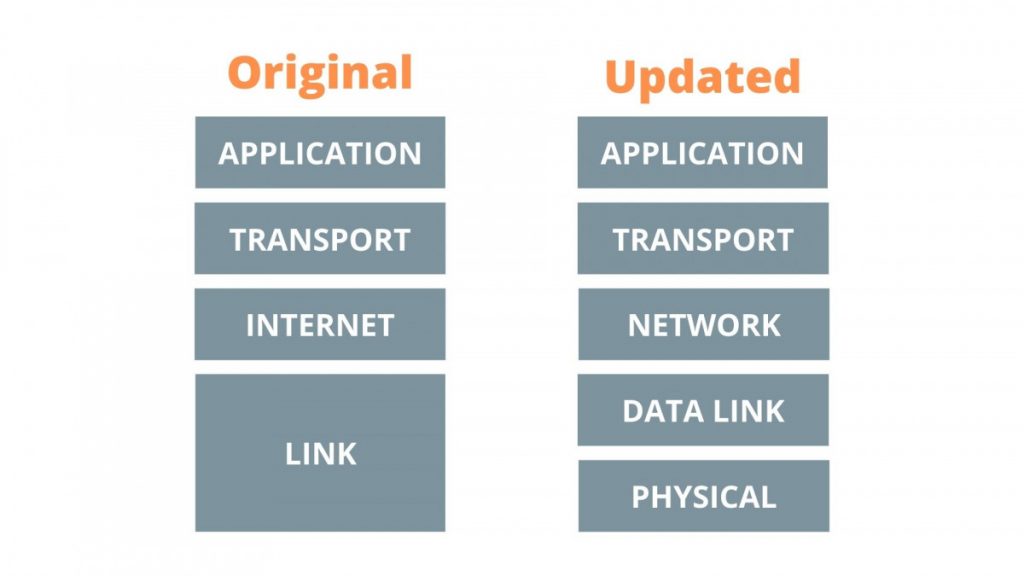
For the updated TCP/IP model, the internet layer of the original model has been renamed to the network layer, and the link layer has been split into the data link layer and the physical layer. All the other layers have stayed the same.
Therefore, I am only going to cover the two new layers here:
Data Link Layer
In the updated TCP /IP model, the data link layer now contains the source and target MAC address, and is responsible for the resolution of the target device’s MAC address (mapping logical IP addresses to physical MAC addresses).
Physical Layer
As the name suggests, this layer represents everything we can feel and touch, for example, cables or network interface cards.
Basically, it is all about physically transporting data from one device to another device.
How does the TCP/IP model work?
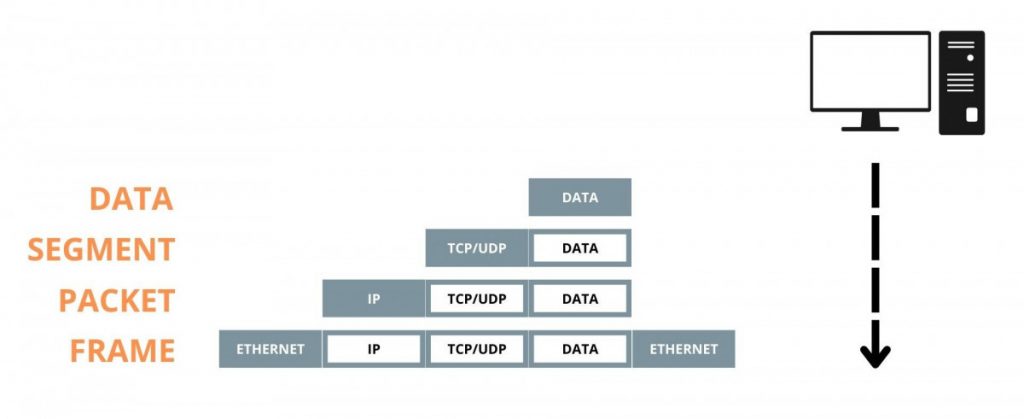
If we want to send some data to another computer, we start by adding the actual data (message) at the fifth layer (Application). At this stage, the data is simply called data.
Next, we add the transport information by adding either a TCP or UDP header, which adds source and destination port numbers and a few more bits of information. Now, we call the data a segment.
At the network layer, we add an IP header, which contains the source and destination IP address as well as some other bits of information. At this stage of the model, the data is called a packet.
At the second layer (data link), we add an ethernet header and trailer.
The header mainly contains the source and destination MAC address, whereas the trailer contains some error-checking information. At this stage, our packet becomes a frame.
Finally, we need to physically transmit the data.
The receiving computer now decapsulates the data going in the opposite direction.
What is the OSI model?
Actually, we don’t use the OSI model in real life. However, it gets referenced a lot in computer networking. Therefore, it is always good to know what it looks like. In fact, it is very similar to the TCP/IP model:
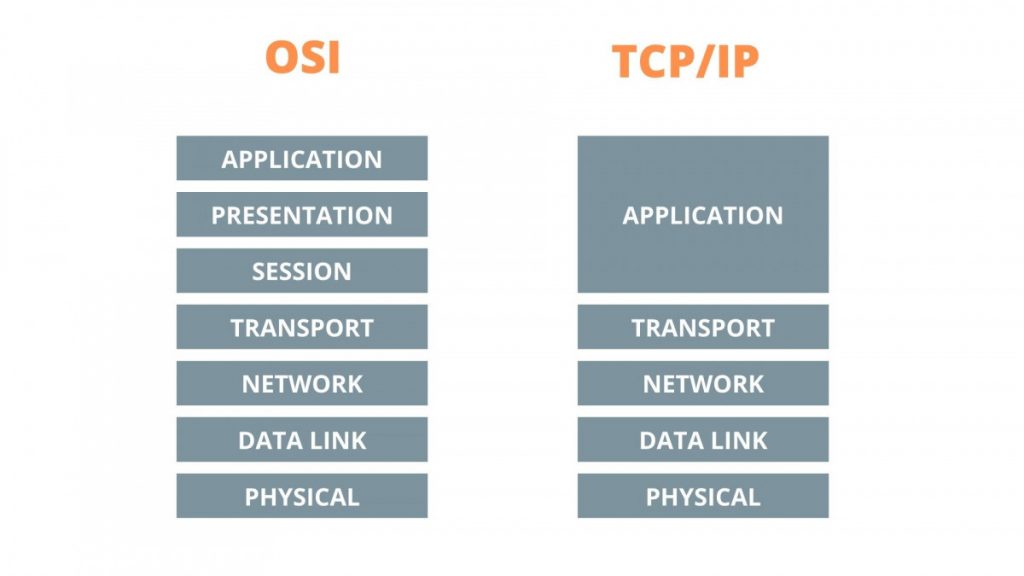
As you can see, the only difference is that the application layer is split into the application, presentation, and session layers.
Conclusion
When dealing with computer networking, the TCP/IP and OSI models get referenced a lot because it is the main part of every connection between multiple devices. Therefore, knowing at least the basics is very important, for example, to be able to troubleshoot networking problems.
Even though the original TCP/IP model has been updated, you will find the original one a lot as the way it works is still the same.
Just keep in mind that the OSI model isn’t used in real life and only serves as a reference.
Thanks for reading!